Checkmarx Jenkins Plugin Compromised by TeamPCP Malware
TeamPCP's supply-chain attack compromised Checkmarx's Jenkins plugin.

Checkmarx, known for application security testing, recently faced a serious security breach. Over the weekend, the company warned that a rogue version of its Jenkins Application Security Testing (AST) plugin was uploaded to the Jenkins Marketplace. It was compromised with credential-stealing malware, claimed by the TeamPCP hacker group.
Jenkins, a popular CI/CD automation tool, integrates with various development environments to automate software building and deployment. The Checkmarx AST plugin is popular for adding security scanning to these workflows.
The Compromise Uncovered
TeamPCP infiltrated Checkmarx's GitHub repositories, exploiting credentials from a supply-chain attack on Trivy in March. With access, they inserted malicious code into the Jenkins AST plugin, spreading info-stealing malware.
Checkmarx confirmed that the altered plugin was uploaded outside the official release pipeline and lacked the usual git tag or GitHub release markers. Affected users should revert to version 2.0.13-829.vc72453fa_1c16 or earlier.
Implications and Recommendations
This attack is the third supply-chain breach impacting Checkmarx since late March. TeamPCP retained access for a month, targeting tools like Docker and VSCode with similar payloads. If you downloaded the compromised plugin, assume your credentials are compromised. Rotate secrets and watch for unauthorized access.
Checkmarx says its GitHub repositories are isolated from customer environments, reducing risk to customer data. They've communicated with customers and provided guidance via their Support Portal.
Background:
Supply-chain attacks like TeamPCP's are increasingly common, targeting vulnerabilities in software distribution. By compromising updates or plugins, attackers can infiltrate development environments, leading to data breaches and system compromises.
What's still unclear:
- What exactly the rogue Jenkins plugin does upon installation.
- If other Checkmarx tools are compromised.
- The full extent of accessed or stolen data.
Why this matters:
This incident shows the persistent threat of supply-chain attacks to software security. As CI/CD tools are key to modern development, their integrity is crucial. Organizations must audit their software supply chains and address vulnerabilities swiftly.
More from Security

GM Agrees to $12.75M Settlement Over Driver Data Sales in California
GM strikes a $12.75M deal with California over claims of illegal driver data sales, spotlighting privacy enforcement.

iOS 26.5 Update Addresses Over 50 Security Vulnerabilities—Update Now
Apple's iOS 26.5 fixes over 50 security flaws. Update your iPhone now to stay secure.

Malware Disguised as OpenAI Found on Hugging Face
A fake OpenAI repo on Hugging Face pushed malware disguised as AI tools, targeting Windows users with info-stealing tactics.

US Men Sentenced for Assisting North Korean IT Espionage
Two Americans were sentenced for helping North Korean agents pretend to be IT workers in a massive espionage and financial scam.
Don’t miss these

OpenAI Launches Daybreak: A New AI Initiative for Cybersecurity
OpenAI rolls out Daybreak, an AI initiative to catch vulnerabilities before hackers do. It uses Codex and other models for better security.
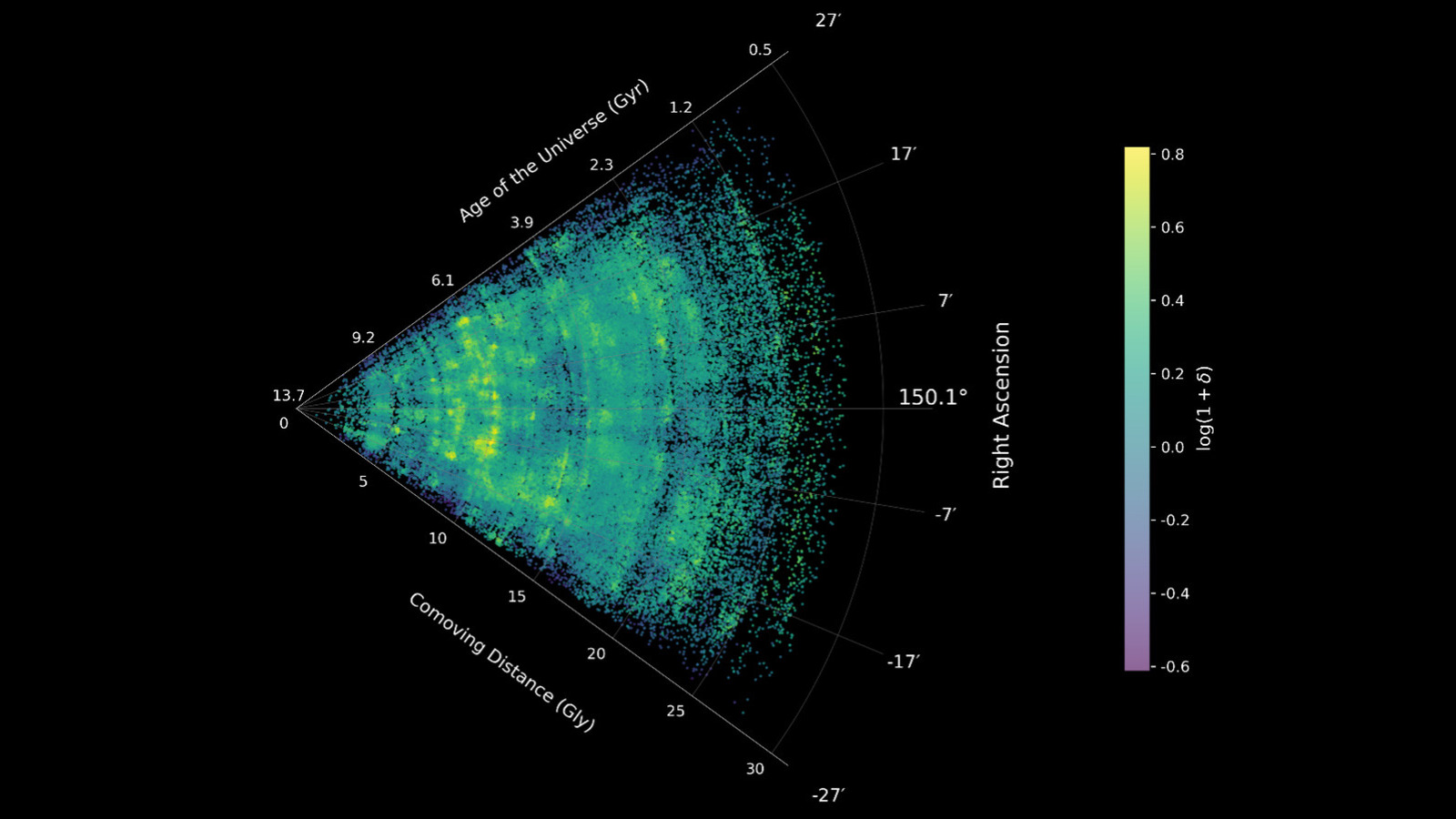
James Webb Telescope Reveals New Insights into the Cosmic Web
Astronomers have used the James Webb Telescope to map the cosmic web, revealing intricate details of the universe's structure.

Anker Nano GaN Charger Now Just $22: Compact Power for All Devices
Anker's Nano GaN II charger packs 65W in a tiny form, now at $22—perfect for travel and versatile charging.

Vin Diesel Announces Four Fast & Furious Shows Coming to Peacock
Vin Diesel announces four Fast & Furious TV series on Peacock, marking a new venture for the franchise.

Apple Gets Court OK to Seek Samsung Docs in Antitrust Fight
A U.S. court has given Apple the green light to request documents from Samsung in South Korea for its DOJ antitrust case.

Lego Batman Game Leak Sparks Spoiler Fears
Early access to Lego Batman: Legacy of the Dark Knight on Xbox via Walmart codes raises spoiler concerns ahead of the official launch.